What's new?
An overview of the new features introduced in each release. For more detailed information about each release, see the release notes.
Version 6.8
The way users are able to authenticate in Blue Prism has been enhanced, providing more flexibility and supporting more complex Active Directory environments. When creating a new Blue Prism database, administrators are able to choose between two types of environments:
- Multi-authentication environment – Builds on the existing Blue Prism native authentication and additionally supports a new Active Directory authentication method where roles are mapped to individual users in Blue Prism. Active Directory users in a multi-authentication environment can be contained across multiple domains and forests with appropriate domain/forest trusts in place. All Blue Prism native authentication environments will be updated to support multi-authentication from 6.8. Learn more
- Single-authentication environment – Supports Active Directory authentication where users log in via Active Directory only and roles are mapped to Active Directory security groups. Active Directory users in a single-authentication environment can be contained across multiple domains but only a single forest. This was referred to as Active Directory Single Sign-On in previous versions of Blue Prism. Learn more
Integration with applications and web pages presented in Chromium-based versions of Microsoft Edge is now supported via the Blue Prism Chrome browser extension. Users must manually install the Blue Prism Chrome extension from the Chrome store to be able to use the Microsoft Edge Chromium-based browser. Learn more
The Blue Prism interactive client user interface and product help are now available in German. When starting Blue Prism, the user interface automatically displays in the locale of the operating system for supported languages, using localized formats for elements such as dates, times, and numbers. A drop-down has also been added to the login screen, allowing users to select a language for the client. The in-product help has also been fully translated to Japanese, Simplified Chinese, French, and German, and when accessed, will match the language of the user interface.
A new search box has been added at the top of the left-hand pane in the following areas of the Blue Prism interactive client, which makes it easier for users to find and filter existing items in the corresponding navigation tree:
- Studio > Processes and Objects
- Analytics > Tile Library
- System > Resources - Management
- System > Workflow - Work Queues
- System > Security - Users
Blue Prism now supports integrated Windows authentication when authenticating against the Blue Prism database. This introduces the ability to use Data Gateways in deployments of Blue Prism that use a database that only supports Windows authentication. Changes have been made to support this enhancement on the following screens:
- Data Gateways - Settings – Users now have the option to use Windows integrated security when connecting Data Gateways to the Blue Prism database. Users can now select to connect Data Gateways to the Blue Prism database using either a SQL native user account (stored within a Blue Prism credential record) or using Windows authentication. Learn more
-
Server Configuration Details – The existing Data Gateways settings in the Details tab in BPServer have been moved to a new Data Gateways Settings tab. As part of this move, the Data Gateways Process Port setting has been renamed Communications Port. Users also have the option to specify the Windows authentication user used to access the Blue Prism database. Learn more
- Data Gateways output wizard – A new page has been added, which enables users to choose which session log fields to include for the selected output type. Learn more
To enable users to easily compare stages in Process and Object Studio, it is now possible to open the properties dialogs of multiple stages in a single process or object simultaneously. Learn more
A number of enhancements have been introduced throughout the Blue Prism interactive client to improve the overall usability of the Blue Prism user interface:
-
Buttons, text boxes, and radio buttons now display a yellow highlight when selected with the cursor or the keyboard.
- A new mouseover state has also been added to buttons, text boxes, and radio buttons.
- In Process and Object Studio, the tab for the currently selected page is highlighted with white text on a blue background.
- In Control Room, the dividers between panels become gray on mouseover and are highlighted in yellow when the cursor is focused on them. The divider positions are now retained when users navigate to a different tab, or log into a different environment, and then return to the Control Room.
Version 6.7
Blue Prism application servers store some information within local configuration files. This includes database connectivity and encryption scheme data. In order to provide greater levels of protection of the data within the configuration files, users can secure Blue Prism application server configuration data using certificate encryption. Certificate encryption allows more robust encryption of the server configuration, which reduces the risk of malicious users accessing customer data.
Further details on using certificate encryption for the Blue Prism application server configuration can be found in the Configure server configuration file encryption settings.
A new server-based HTML5 version of the help provides users with a more contemporary, easily accessible user interface that includes enhanced features and provides a better user experience. The new help can be viewed on multiple devices and has a responsive, flexible layout. As the help is no longer contained within product releases, the content can be updated as and when required, ensuring the information is accurate, up-to-date, and addresses the needs of users.
Release notes, the installation guide, and a number of other feature guides can now be accessed from the online help. The content is available in Japanese, Chinese, and French, automatically reflecting the language selected in the Blue Prism user interface. The online help for all languages can be accessed using the following links:
For more information about the content of this help release see Help version. Also see Using the help for more information about the functionality of the help system.
A new charting tool (LiveCharts) has replaced the existing tool (MetroCharts), making the charts displayed on the Blue Prism dashboard clearer, more intuitive, and interactive. Any existing charts are automatically updated using the new chart styles.
A line chart type, which is compatible with all data types and enables users to visualize data comparisons and trends is also available.
The Blue Prism Interactive Client user interface and product help are now available in French. When starting Blue Prism, the user interface is automatically presented in the locale of the operating system for supported languages, using localized formats for elements such as dates, times, and numbers. A drop-down has also been added to the login screen, allowing users to select a language for the client. The in-product help has also been fully translated to Japanese, Simplified Chinese, and French and when called, will match the language of the user interface.
The Digital Exchange tab has been added to Blue Prism, which when clicked, opens the Blue Prism Digital Exchange.
The My Profile tab allows users to quickly change their password and sign out.
Version 6.6
Blue Prism is compatible with devices that enforce Federal Information Processing Standards (FIPS) compliant algorithms. The Blue Prism application server, interactive client, and runtime resources check to see if the security policy to use FIPS compliant algorithms for encryption, hashing, and signing is enabled on devices.
Where the FIPS compliant security policy is enabled:
- Non-FIPS compliant encryption schemes cannot be selected in the Encryption Scheme and Work Queue system settings on the interactive client.
- Non-FIPS compliant encryption schemes cannot be selected when configuring an encryption scheme for application servers. Application servers that are already configured with a non-FIPS compliant encryption scheme will not run and log an error.
- Any AutomateC commands that call user configured schemes that are not FIPS compliant cannot be run.
- Advisory messages display when attempting to log into interactive clients or start a runtime resources that reference a database with a non-FIPS compliant encryption scheme. It is still possible to log into such devices but processes and objects that reference a non-FIPS compliant encryption scheme will not run until the scheme is updated.
Version 6.5
Data Gateways provides an easy-to-use, centralized method of pushing data out of Blue Prism for use in external systems for monitoring and reporting, long-term data storage, and to feed machine learning models. Advanced configuration methods allow data to be directed to any required target. The data can be visualized and analyzed to provide valuable insight about Blue Prism environments without having to manually build similar capabilities into each relevant process automation.
By providing the ability to store data outside the Blue Prism database, organizations can use Data Gateways to support flexible data storage requirements. For example, an organization might want to save all their session data outside the Blue Prism database, or they might choose to store data in the database for a shorter period of time, pushing out a copy of that data for longer term data storage.
Settings are applied to determine what data will be processed by the Data Gateways engine, and a configuration defines the outputs to which data will be pushed. Data from session logs, published dashboards, process stages, and work queue analysis can be sent to a variety of external outputs – HTTP endpoints, external databases, third-party analysis tools, and flat files – providing flexibility and control over data analytics and storage.
The Data Gateways engine utilizes a number of Logstash components to send session log data to configured outputs.
To set up data gateways, a number of Logstash components must be installed on the application server – available in a separate installer from the Blue Prism customer portal. The Data Gateways must also be enabled on the application server in the Server Configuration screen where the port that the application server will listen on must also be specified. Learn more
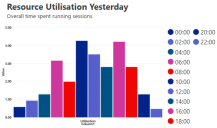
Work queue snapshots take periodic snapshots of work queue metrics at defined intervals and compare current data with the data from previous snapshots to analyze differences and track trends. The trends can be visualized in dashboard tiles, sent to Data Gateways, or externalized to management information and business intelligence tools, to provide a quick and easy way to gain a better understanding of:
- The level of items to be worked
- The number of items worked
- The number of exceptions
- Unusual spikes in queue volumes
For example, work queue snapshots could be used to find out how the current average case duration compares to a typical Monday morning, or to track how the number of cases in your queue on a Friday morning has been fluctuating over the past seven days.
The Collect utilization and productivity statistics option must be enabled in Settings > Reporting.
Snapshot configurations, created in System > Reporting > Work Queue Snapshots, determine which queues are included in the data and at what frequency the snapshot is taken. All snapshotted data is kept for 28 days, after which it is automatically deleted.
Snapshot analysis
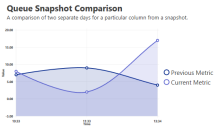
Two data sources are available that allow snapshot comparison data to be visualized in dashboard tiles:
- Queue Snapshot Comparison – Compare the current data for a specified metric with that of a given day.
- Queue Snapshot Against Trend – Compare the current data for a specified metric with averages calculated over a selected period.
Examples of metrics that can be used in comparisons are total items, items pending, and average idle time. Learn more
To ensure compatibility with evolving network infrastructures, support for IPv6 connections has been introduced. Blue Prism can be deployed in environments that utilize IPv4 or IPv6 network protocols for all connections as well as those that use a hybrid approach, utilizing a combination of both protocols. This allows all Blue Prism components – runtimes, clients, application servers – to connect using the preferred or most suitable method.
To support this functionality, the Binding section of the Blue Prism Server Configuration Utility has been updated to accept IPv6 addresses as an alternative to the currently available options of hostname or IPv4 address. Where devices are configured to support both IPv4 and IPv6 connections, IPv6 will be used by default. Learn more
The Blue Prism interactive client user interface and product help are available in Japanese and Simplified Chinese. When starting Blue Prism, the user interface is automatically presented in the locale of the operating system for supported languages, using localized formats for elements such as dates, times, and numbers. A drop-down has also been added to the login screen, allowing users to select a language for the client. The in-product help has also been fully translated to Japanese and Simplified Chinese and when called, will match the language of the user interface.
The Login Agent has been updated to include an SAS proxy that can send programmatic Ctrl + Alt + Del key sequences where if there is a requirement to do so. New options for configuring this feature have been added to the Login Agent installer. Learn more
Version 6.5 is installed with Tesseract OCR V4.0.0. Tesseract OCR leverages pattern matching and complex, language-based text recognition and is provided to assist with reading on-screen text and identifying form labels.
Language packs
Blue Prism ships with Tesseract English language files. Language packs for other languages that will be processed must be downloaded and distributed to each device where Tesseract will operate.
Tesseract language packs from versions prior to version 6.5 are not supported with this release. If upgrading to version 6.5, new language packs must be installed. Directions on how to complete this step are provided in the product Help. The language packs can be downloaded from: https://github.com/tesseract-ocr/tesseract/wiki/Data-Files
Operating settings
As part of the 6.5 upgrade, the following options for Tesseract V4.0.0 are provided in the System > Settings:
- 0 – Legacy engine only – Operates Tesseract V4.0.0 in compatibility mode that mimics the behavior of V3.05.01 – ideal if troubleshooting following an upgrade.
- 1 – Neural nets LSTM engine only – Operates with the OCR engine that uses a neural network system based on Long Short-Term Memory (LSTM).
- 2 – Legacy plus LSTM engine – Operates in compatibility mode with added support for LSTMs.
- 3 – Default, based on what is available – Uses the best available engine for the version of Tesseract that is currently in use in the installed version of Blue Prism.
Reverting to a previous version of Tesseract
Blue Prism 6.5 can be manually configured to work with Tesseract V3.05.01 – the version of Tesseract that was provided with earlier versions of Blue Prism v6.
This is achieved by adding the Tesseract V3.05.01 executable to the Blue Prism install location. To achieve this, complete the following steps on each runtime resource and Interactive client used to design automations that use Tesseract.
-
Navigate to the Tesseract folder in the install location of Blue Prism 6.5:
C:\Program Files\Blue Prism Limited\Blue Prism Automate\Tesseract\
Adjust this path if a custom install location has been used.
- Delete the tesseract-4.0.0.exe file.
-
Add the executable file for the V3.05.01 version of Tesseract, obtained from the same install location for all Blue Prism versions from 6.0 to 6.4.2.
The filename for the V3.05.01 Tesseract executable is tesseract.exe – it does not include the version number.
-
Ensure that the Application Manager Setting in System > Settings is set to 3 – Default, based on what is available.
- Install the language packs appropriate to the Tesseract V3.05.01.
When Blue Prism is next started, it now uses the V3.05.01 version of Tessaract.
The Google Sheets VBO provides an easy-to-configure method of interacting with Google Sheets, enabling process automations to create and update spreadsheets. Automations can interact with a single cell or range of cells to get and set values or formulas within the specified cells.
The following actions are included in the VBO:
- Append Data – Adds the given data to a specified cell or range of cells.
- Clear Range – Clears all data from the a specified cell or range of cells.
- Get Range Values – Retrieves values or formulas from a single cell or range of cells.
- Set Range Values – Sets the values or formulas for a single cell or range of cells.
- Create Workbook – Creates a new document in Google Sheets and returns its Sheet ID.
To configure and use the Google Sheets VBO, a Google account is required with the Google Sheets API enabled. The associated Google client ID is also required to configure the environment variables needed to access Google sheets for that account.
To operate, the VBO requires a number of DLLs to be placed locally on each device where it will run. To assist with deployment, the Blue Prism Installer contains an option to install the Google Sheets Automation component as part of a custom installation that places these DLLs. Learn more...
Version 6.4
Blue Prism’s Intelligent Automation Skills enable organizations to optimize and democratize AI capabilities throughout the business by creating a smarter, more powerful, digital workforce. Utilizing these skills increases operational agility and improves productivity, transforming the way an organization uses technology to drive business value. Technologies are now easily accessible through an ecosystem of partners, making it simple for organizations to leverage technologies that deliver true operational agility, such as artificial intelligence capabilities, machine learning, and analytics.
A Blue Prism Intelligent Automation Skill is an item of functionality, such as a preconfigured connection to an external service or capability, that has been branded and packaged for use in a Blue Prism process automation. Skills packages typically contain a web API definition but can also include any number of objects, processes, and credentials that support the use of the API definition. Packages can be imported into Blue Prism and subsequently used as stages in objects and processes, providing a quick and effective way of interacting with different technologies without the overhead of having to create and configure the required Blue Prism items. Learn more
Web API functionality provides a configuration interface for natively interacting with systems and services that provide published HTTP APIs. This allows Blue Prism to interact with these services to either provide data to, or to consume the data or services provided by these external systems within an automated business process. The features provided by the Web API functionality allow the most common services to be automated by Blue Prism. Additionally, these capabilities can be extended to cater for bespoke or more complex data structures and authentication mechanisms, through the use of code stages. Learn more...
Blue Prism can be deployed in environments that utilize contained databases hosted on Microsoft SQL Server. Contained databases must be manually created and configured – it may also be necessary to manually apply upgrade scripts rather than using the in-product update database capability. Learn more
Version 6.3
Blue Prism delivers native support for automating Google Chrome and Firefox by utilizing dedicated browser extensions. The extensions allow Blue Prism to interact with web pages and applications presented in Chrome and Firefox.
The Application Modeller wizard has been updated with a new Browser-based Application (Chrome and Firefox) application type that enables Chrome and Firefox elements to be spied and used in navigate, read, and write stages. A new Web Page spy-mode has also been introduced for dedicated use with the extensions. Learn more
Support for Multi-Team Environments has been introduced that allows a user's security role permissions to be refined at group level. This allows permissions to be applied that are specific to groups of objects, processes, and resources, enabling organizations to model increasingly complex security configurations within Blue Prism. Learn more
A new mechanism for validating key instructional communications received by runtime resources has been introduced. This enables the runtime resources to enforce the increasingly granular security model introduced in this version by validating that the user making the request has authority on the specific process and resource to do so. Prior to 6.3 it was the permissions of the account used to authenticate the runtime resource against the environment that were evaluated.
This improved mechanism is enabled by default and is represented by the setting Session Management enforces permission of controlling user. When enabled, the setting disables the legacy programmatic controls: create, delete, and start; and replaces them with createas, deleteas, and startas.
If this setting is disabled, it will be the permissions of the user account used to start the runtime resource that will be validated (rather than the controlling user). This is not recommended and is only provided for backwards compatibility while any scripts that programmatically control the runtime resources are updated to use the recommended mechanism.
Version 6.2
API integrations with leading cloud AI services are now available and can be utilized via a suite of Visual Business Objects (VBOs). The VBOs are available to download as ZIP files from the Blue Prism portal within the Documentation section. The integrations delivered through these VBO enable an even greater level of intelligence to be applied within Blue Prism process automations.
The following API integrations are available for use with Blue Prism 6.2 and above:
- Google Cloud
- Natural Language
- Translation
- Vision
- Microsoft Cognitive Services
- Text Analytics
- Text and Speech Translation
- Language Understanding Intelligent Service (LUIS)
- Computer Vision
- IBM Watson
- Natural Language Understanding
- Language Translation
- Visual Recognition
Blue Prism 6 is certified for use with desktop installations of Excel and Word 2016. Automations which interact with Excel and Word can be used with dedicated Visual Business Objects (VBOs) that are included with the core product. These VBOs will continue to be extended and enhanced throughout the v6 series.
Native support for Microsoft UI Automation (UIA) has been introduced with the addition of a dedicated Spy Mode and UI Automation Navigator. UIA is an accessibility framework that enables Windows applications to provide and consume programmatic information about user interfaces. UIA offers improvements in speed, accuracy and resilience over Active Accessibility (AA) when creating automations. AA continues to be supported as a native spy-mode.
UI Automation Spy Mode
The UIA Spy Mode can be used to identify visual elements of the target application and add them to the application model, in the same manner as other native spy-mode options.
UI Automation Navigator
The UI Automation Navigator provides a number of views which can be used to traverse the UI model of the application. The navigator can be accessed from within the Application Modeller once the target application has been launched.
The available views which are available within the Automation Navigator are categorized as 'Raw', 'Control' and 'Content'.
The model can be filtered by entering a search term in the filter box above the model. On pressing enter or after stopping typing for a short while, the tree will be filtered such that it will only contain elements whose names or selected attributes contain the filter text.
Raw View
The full tree of automation elements which closely follows the native programmatic structure of an application. This is the most detailed view available.
Control View
This is a subset of the raw view. It contains elements which show information to the user or enable the user to perform an action. It can also contain non-interactive UI elements which contribute to the logical structure of the UI, such as list view headers, toolbars and menus. Non-interactive elements used do not appear in the control view.
Content View
This is a subset of the control view. It contains elements which convey information in a user interface, including UI elements that can receive keyboard focus and some text that is not a label on a UI element.
A number of new options have been introduced when exposing processes and objects as web services:
- Document/literal encoding can now be enforced when exposing a web service in the user-interface and also via the command line with a /forcedoclitencoding switch. This will force all actions (including Initialize and Cleanup) to use the specified format. If this enforcement is not selected, the Initialize and Cleanup actions will use RPC encoding, and the encoding for custom actions will be determined based on whether a collection data type is defined as an input or output parameter.
- The web service address location that will be displayed within the WSDL of the service can now be optionally configured with an override address. This option is configured through use of the /wslocationprefix command line switch when starting a runtime resource. If no location is set, the resource will continue to be addressed either by the machine (short) name or FQDN as configured under System Settings.
- When calling a process or object which has been exposed as a web service, outputs that are simple types no longer have an empty XML namespace (xmlns=""). For backwards compatibility, when exposing a process or object as a web service, users can specify that if Blue Prism determines that RPC encoding should be used, that legacy name spacing should be used.
Version 6.1
Blue Prism have contracted with Veracode, the industry-leading software vulnerability scanning organisation, to undertake regular product vulnerability analysis using an industry-standard trusted third-party supplier of application vulnerability analysis.
Blue Prism Version 6.5 has been certified to Vercode Level 5 and has passed the OWASP Top 10 assessment. Each subsequent release within the v6 series is evaluated against the same criteria with the target compliance certifications outlined in the appropriate release notes.
Blue Prism remains committed to ensuring compliance with the latest codes and standards for data security. By leveraging an independent third party like Veracode we strengthen our security. Through continuous testing and vetting, and ensuring we have the proper tools and processes, Blue Prism continues to deliver software robots that are secure, reduce the risk of data breaches, and meet compliance requirements in a wide variety of industries.
A compliance highlight summary report is available upon request via Product Support.
For more information about Veracode vulnerability analysis: https://www.veracode.com/products/binary-static-analysis-sast
Version 6.0
Several Surface Automation techniques have been greatly enhanced to derive the following benefits:
- Less complexity when designing automations.
- Reduced skill set required to build automations.
- Increased performance and resilience of automations as they execute.
The improvements can be grouped based on the area of the product where they are visible:
- Region Editor – The mechanism for defining how to locate regions has been extended. It is now possible to:
- Easily select whether the region should be found based on coordinates or an image match. The image match location method is intended for use with form elements with static content such as labels, icons and buttons. Coordinate regions are intended for elements that contain dynamic content such as text, check boxes and combo-boxes.
- Select the search area for a region. Image regions can be searched for anywhere on the screen, in a fixed position, or in a position relative to another region. Co-ordinate regions are searched for using a fixed position by default and can also use the relative search method.
- When using image matching and a fixed position, a search area around the position can be defined to cater for situations where the image is out of position within a defined tolerance. A larger potential search area will entail a less efficient search detection.
- When using relative positioning, the run-time search area for the region will be dynamically adjusted based on the actual location of the parent item. Both Image and co-ordinate-based regions can be set as relative elements.
- Set an RGB color tolerance range for image regions. This allows for variance in the RGB values of the image pixel colors at run time.
- Convert the image to greyscale. Suitable for searching and identifying image regions when color alone cannot be relied upon.
- Process Development – Process development studio includes improvements to reduce the complexity when building resilient processes:
- A new check exists condition can be used in Wait stages to check that an image region is present before continuing.
- An interval can be set between actions within a navigate stage.
- An interval can be set between individual keystrokes in Send and Press Key actions within a Navigate Stage. (Global Send Keys, Global Send Key Events, Window Press Keys, Window Press Keys with ALT).
When using the Generic HLLAPI connector for mainframe emulators, it is now necessary to select the API code page that the emulator is configured to use. This enables interactions with mainframe emulators configured to use a wide range of locales, including those which contain double-byte character sets. Backwards compatibility is provided for existing processes, which will default to the ASCII encoding translator.
Interactions with mainframe emulators which display text in a Right to Left (RTL) order has also been enhanced with the introduction of an RTL option in the spying context menu. When enabled, the location of the spied elements will be calculated based on the target RTL display.
A new Analytics capability is provided, which extends the previous Dashboard functionality. It enables improved metrics and the ability to configure Dashboards and session information to be directed to external Analytics and monitoring systems, for monitoring or aggregation of metrics across multiple environments. This is achieved through two new mechanisms:
- Published Dashboards: a new type of dashboard that enables the corresponding metrics to be captured within the application server Event Log, for collection by an external monitoring or analytics tool (such as Splunk). A new Design Published Dashboard permission has been provided.
- Fork session log information to an external target. Initially this mechanism will support pushing session log information to the Splunk HTTP listener.
Additional configuration at the Blue Prism Server is required to enable both of the above features. Consideration should be given to the level of logging being performed if enabling Splunk integration of session logs, as high levels of logging may impact process performance.
To make Published Dashboard data available in Splunk, the following must be in place:
- A Blue Prism server which has been appropriately configured for external logging.
- At least one Published Dashboard has been created with tiles containing data to be ingested by Splunk.
- Blue Prism has been added to the Splunk Local Event Log Collection.
Additionally, to make session log data available within Splunk, the following steps must be completed:
- A HTTP Event Collector has been configured in Splunk and a token value generated. Further information on how to complete this set-up process can be found at: http://dev.splunk.com/view/event-collector/SP-CAAAE6M.
- The token value has been added to the appropriate configuration file.
Version 6 is installed with Tesseract OCR V3.05.01. Tesseract OCR leverages pattern matching and complex, language-based text recognition and can be used where it is not appropriate to use the native character recognition engine to interact with on-screen text. Tesseract language packs from versions prior to Version 6 are not supported with this release. If upgrading to Version 6, new language packs must be installed.
The language packs can be downloaded from: https://github.com/tesseract-ocr/tesseract/wiki/Data-Files
Version 6 has reference architectures for Microsoft Azure and Amazon AWS cloud deployment patterns. The disablement of Windows Communication Foundation (WCF) server communication method makes the deployment on cloud easier and more scalable. Full support for additional capabilities, such as load balancing and NAT, has also been enabled. Users should refer to the relevant Cloud Reference Architecture documentation on the Blue Prism User Portal for further guidance on these topics.
Several improvements have been made which provide greater visibility and ease of management of the workforce. These improvements include:
- The Session Management pane now provides multi-select filters for processes and resources, and subject to being enabled, the session management pane is now auto-filtered based on user selections in the processes and resources panes.
- It is now possible to set a maximum time that a process can spend on a given stage before entering a warning state. The warning is configured on a system-wide basis with the option to define an override value per stage.
- The latest stage that was started in a process (along with the start date and time) is now clearly indicated within session management.
- Navigating away from the Control Room no longer causes the selected resource session view to be reset.
- A more prominent indication of which resource is the current resource pool controller.
- The Workforce Availability tile has been updated to more accurately reflect the status of all resources, including data on how many are logged out, working, idle, missing and offline.
The Resources panel in the Control Room now contains more detailed information about each runtime resource. The changes include:
- A new mechanism for displaying the state of the resource such as whether the runtime is idle, running, offline, missing; as well as the number of sessions that are running on each device. This is derived based on runtime resources proactively providing relevant information on a regular basis.
- Resources which are expectedly offline are now shows as missing, and the total time that has elapsed since the last successful connection is displayed with an upper limit of 5 minutes.
- If a resource has been set to Private, the user account which to which it is assigned is displayed.
- The connection state information that indicates whether a direct (instructional) connection can be established from the control room to a given runtime resource is now within the right-hand columns in the pane.
Exception stages can now be set to save a screen capture. When utilized in a production environment, this feature can help troubleshoot and resolve resource processing issues in a timely yet secure manner.
When taken, the screen capture is saved with the date and time of the exception, the name of the resource and the name of the process or object in which the exception occurred. When using this feature, the following points should also be considered:
- The functionality is enabled/disabled via a system-wide setting.
- Screen captures can only be viewed by users with the appropriate permission.
- The screen capture functionality requires that a default encryption scheme has been configured and is valid.
- Only the latest screen capture per runtime resource will be stored.
Customers can opt for CyberArk Application Identity Manager for credential management as Blue Prism is fully certified for CyberArk integration including all feature / functionalities inherent in CyberArk Application Identity Manager.
Provided as a native .NET Framework 4 application, support is now provided for advanced users wishing to reference the latest .NET DLLs whilst maintaining the compatibility for installing the application on a wide range of modern operating systems.
Operating systems that do not support .NET 4.7 can no longer be used with Blue Prism.
The connection modes available when configuring a Blue Prism Server; and when configuring a Blue Prism client to connect via a Blue Prism Server have been extended to offer Windows Communication Foundation (WCF) options. This offers increased control over the encryption that is applied to the communication channel.
The connection mode options which can be chosen in Version 6 include:
- WCF: SOAP with Message Encryption & Windows Authentication
- WCF: SOAP with Transport Encryption & Windows Authentication
- WCF: SOAP with Transport Encryption
- WCF: Insecure
The various WCF modes provide subtly different functionality and support. The table below provides a visual comparison of the key features:
- Transport Mechanism: the type of transport mechanism used to connect the client and server end-points.
- Encrypts Data: whether the mode natively encrypts the data transmitted.
- Requires Trusts: whether the client and server must reside within a command AD network infrastructure.
- Supports SSO: whether Single Sign-on for Blue Prism is supported.
- Requires certificates: whether a server-side certificate needs to be deployed.
|
Mode |
Transport Mechanism |
Encrypts Data |
Requires Trusts |
Supports SSO |
Requires Certificates |
|---|---|---|---|---|---|
|
SOAP with Message Encryption and Windows Authentication |
SOAP over HTTP |
Yes |
Yes |
Yes |
No |
|
SOAP with Transport Encryption and Windows Authentication |
SOAP over HTTPS |
Yes |
Yes |
Yes |
Yes |
|
SOAP with Transport Encryption |
SOAP over HTTPS |
Yes |
No |
No |
Yes |
|
Insecure |
SOAP over HTTP |
No |
No |
No |
No |
To accommodate the addition of WCF server communication methods, several changes have been made to the Blue Prism Server configuration interface to improve usability and ease of configuration. Some of the main changes to the Server Configuration screen are highlighted below:
- If the server service is configured as a WCF endpoint, an alert is presented if the user configured to start the service does not have theappropriate local admin permissions.
- When configuring a server service, if a valid Windows Service has not already been configured, the user is alerted via the configuration interface.
- If a Windows Service had not previously been configured for a server profile, the user is given the option of using an on-screen Create Service button.
- An interface is provided for selecting which installed server certificate to associate with the Blue Prism server service, when using a WCF connection mode with transport encryption.
After a successful upgrade to Version 6, it is strongly recommended that the server communication method is changed to WCF. To complete this process, the following steps should be taken:
- Select an appropriate WCF communication method which aligns with the deployment architecture.
- If using a WCF method with Transport Encryption, generate the required server certificate per server.
- Stop all component devices.
- Make the necessary server configuration changes.
- Start the server.
- Update the connection settings on all components.
 Docs
Docs